Fudcrypt builder, like WSH RAT builder uses HWorm. The last version of the builder from 24th of September provides some interesting insight:

In the case of Fudcrypt, compared with WSHRAT, the HWorm payload, in VBS, is not included as a resource, but is pull from a remote URL. This payload is then obfuscated with a routine. The code of the routing is below:
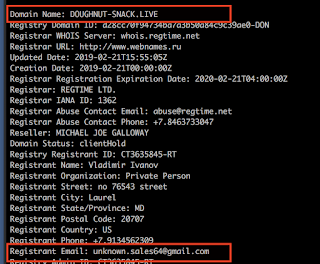
The interesting part is that the plain text payload (HWorm) contains "live:unknown.sales64". Unknown.sales64 is the actor behind WSHRAT and the skype ID is always in the header of the HWorm in VBS and JS.
The User-agent is also "WSHRAT" .
In terms of the code and functionality of the HWorm used by Fudcrypt, is not the latest version used in WSH RAT. It is possible Fudcrypt actors don't have access to the latest version of the WSHRat where the newer code is used
With Fudcrypt it is also possible to 'crypt' Java files. In order to do that, the builder contains the full Java JRE environment:
The code to create and 'crypts' the Java code works in a similar way than the VBS.